Executive View | Digital Lending Control
Midnight Digital Heists | Kenya | Executive Strategy Brief
Licensed by CBK. But Can Your Backend Survive Midnight?
Why the real management question for a digital lender is no longer just how fast it can approve and disburse, but how safely it can detect, stop, explain, and recover from after-hours digital theft, impersonation, and weekend fraud.
For CEOs, CIOs, CTOs, COOs, heads of risk, compliance leaders, fraud teams, and digital lending executives | April 2026 | Editorial feature
The management question is this:
Your CBK licence lets you enter the market. It does not protect you at 00:37 on a Sunday.
As of December 30, 2025, CBK had licensed 195 digital credit providers after receiving more than 800 applications since March 2022. By November 2025, those licensed players had already issued 6.6 million loans valued at KSh 109.8 billion. At the same time, Kenya’s digital rails are operating at national scale, with 48.6 million mobile money subscriptions by end-September 2025, while the Communications Authority later reported that more than 4.5 billion cyber threat events were detected between October and December 2025.
That is why midnight digital heists matter. They compress every weakness at once: thin staffing, faster payout expectations, impersonation attempts, compromised devices, social engineering, configuration abuse, and delayed human escalation. What looks like a cyber incident in the morning is usually a backend design failure the night before.
195 Licensed DCPs
The field is now large and regulated, which means operational weakness is no longer excused as startup chaos.
KSh 109.8B Lent
Scale magnifies risk because every weak control becomes expensive when the rails are active around the clock.
4.5B Cyber Threats
The online environment is hostile and after-hours abuse should be treated as an operating assumption, not an edge case.
48.6M Mobile Money Subs
Kenya is a real-time digital market, so speed, convenience, and attack surface rise together.
1. The licence is the beginning. Midnight is the real test.
Many management teams still think of licensing as the hard part and operations as execution detail. That is backwards. Once licensed, a digital lender is no longer being judged only on whether it can originate credit. It is being judged on whether it can run a disciplined, defensible, always-on digital operation that stands up to fraud, customer complaints, audit review, and regulatory scrutiny.
The CBK framework already points in this direction. An applicant must describe its ICT system and obtain independent assurance on those systems. It must provide AML/CFT policies, data protection procedures, consumer redress mechanisms, pricing logic, and governance documentation. Once operating, it must generate receipts, provide statements on request, resolve customer complaints, maintain complaint records, ensure business continuity, and use secure and reliable systems that preserve confidentiality, integrity, and availability.
That should tell top management something important. A digital lender is not just an app business. It is a control-stack business.
2. Midnight digital heists are architecture tests disguised as incidents.
The most dangerous digital theft is rarely loud at the beginning. It often starts as something small enough to look normal: a password reset, a new device, a limit change, a profile edit, a suspicious but not impossible disbursement pattern, a silent rules tweak, or a privileged user doing the wrong thing at the wrong time.
Weekend and after-hours attacks are especially dangerous because the institution is operating with thinner human oversight. Customers may be asleep. Call-backs take longer. Escalation trees move slower. Treasury, risk, fraud, support, and technology may not all be looking at the same screen. That is exactly where impersonation, payout abuse, and rule manipulation thrive.
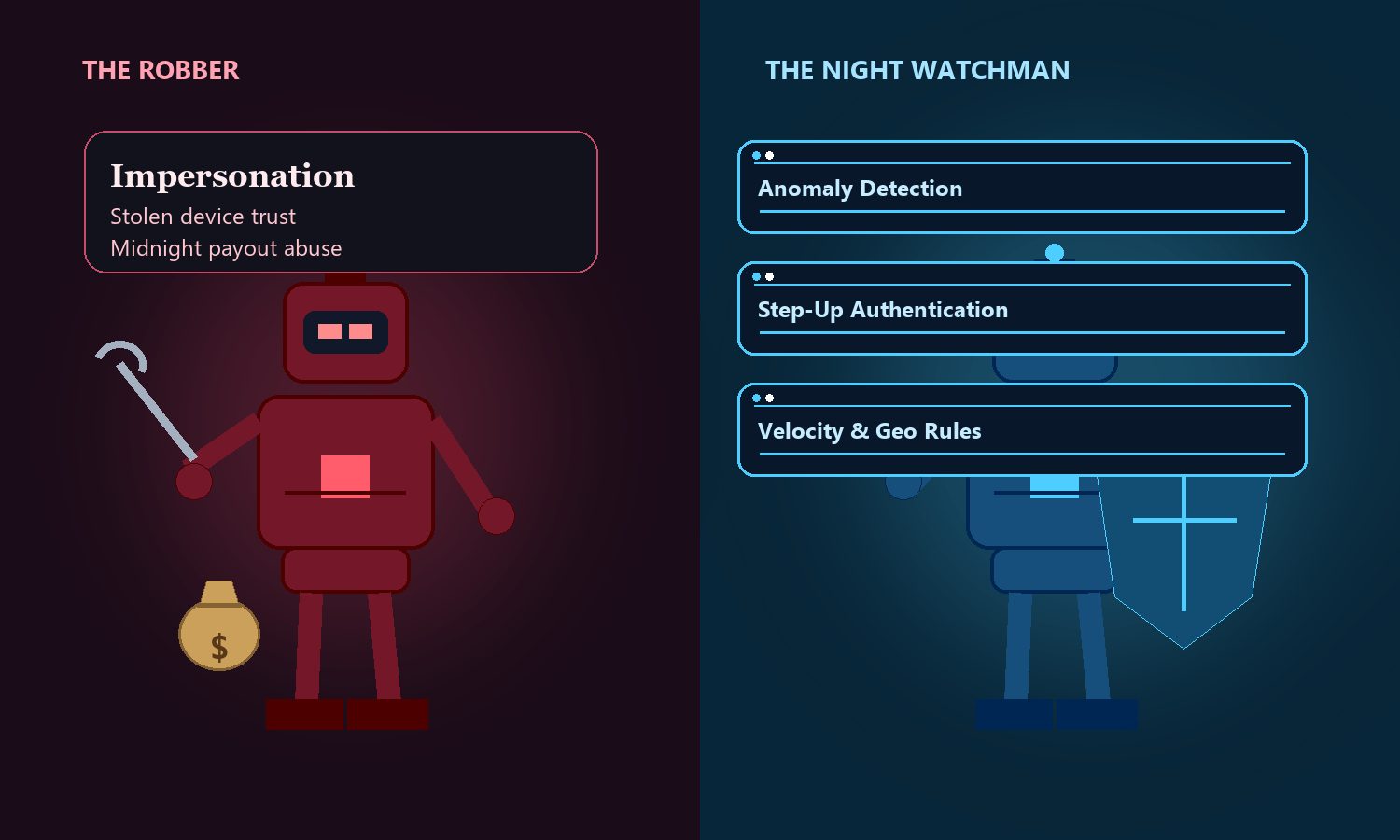
Impersonation
A fake actor borrows real trust through stolen credentials, SIM abuse, device theft, or social engineering.
Payout Abuse
A suspicious disbursement looks routine until velocity, timing, and destination data are connected in real time.
Privileged Change Risk
The attacker may target the controls themselves by changing limits, workflows, alerts, or user rights before money moves.
Your licence is regulatory permission. Your backend is your night guard.
Executive design principle for digital lenders
3. What a licensed digital lender backend must be able to do
If management wants a clean answer to the midnight problem, the backend must support more than booking loans and sending SMS alerts. It must operate as a detection, decision, evidence, and recovery system.
The minimum backend checklist
- Separate actor, device, and session trust: the system should know who is transacting, from which device, under what session pattern, and how that compares to normal behavior.
- Score risk before money moves: disbursements, profile changes, resets, and limit edits should be evaluated in real time, not only investigated after loss.
- Apply time, velocity, and destination controls: the backend should understand unusual midnight activity, repeated attempts, rapid retries, and suspicious payout destinations.
- Trigger step-up, hold, or stop actions immediately: the difference between alerting and protection is whether the system can actually intervene before funds leave.
- Watch privileged users and parameter changes: digital theft is not only a customer-channel problem; it can be an admin and configuration problem too.
- Reconcile channels, balances, and books continuously: wallet movement, bank settlement, loan ledger position, customer statement, and general ledger should not diverge silently overnight.
- Produce receipts, statements, and complaint evidence on demand: when a customer disputes an event, the institution should be able to reconstruct the truth quickly and defensibly.
- Preserve continuity and clean recovery: if there is a failure or breach, backups, failover, audit trails, and recovery sequencing should already be defined and tested.
This is where many lenders get exposed. They buy speed at the front end but leave judgment fragmented at the back end. The result is a fast app sitting on a slow control model.

4. The weekend and after-hours control model management should demand
Midnight protection is not a single fraud rule. It is an operating model. The institution should know what happens when a suspicious transaction hits on a Saturday night, who gets alerted, what the system can freeze automatically, what requires human review, how evidence is captured, and how the morning team receives the case.
What the night shift should orchestrate
- Anomaly detection across logins, resets, disbursements, collections, profile edits, and admin actions.
- Automated response paths such as step-up authentication, temporary hold, transaction delay, or payout suspension.
- Case creation and evidence packaging with timestamps, device data, rule hits, balances, user actions, and system actions.
- Reconciliation checkpoints so the institution knows whether money movement, loan state, and accounting state still agree.
- Morning handoff discipline so unresolved incidents move cleanly from automated controls to risk, fraud, operations, and customer support.
Management should also ask a harder question: if the fraudster is not the customer but an impersonator or a compromised insider, does the platform still notice? If the answer is unclear, the backend is not yet ready for scale.
5. Where Apex Digital Night Guard fits
This is the gap Apex addresses with its Digital Night Guard product. The strategic value of a night-guard layer is not another dashboard. It is after-hours awareness tied to real intervention, so the lender can detect suspicious behavior, escalate intelligently, and take protective action before a midnight anomaly becomes a Monday headline.
Used properly, a Digital Night Guard should sit above the lender’s operational core and watch the events that matter most: risky logins, impersonation patterns, unusual device shifts, disbursement spikes, admin changes, limit overrides, suspicious repayment flows, and any mismatch between customer activity, transaction history, and ledger reality.
That is also where the broader Apex platform matters. A serious lender needs one backbone that can unify customer data, loan operations, workflow controls, reconciliation, accounting discipline, and audit history. If the backend is fragmented, the guard sees fragments too.
What management should expect from a digital night guard
- After-hours anomaly monitoring across customer, device, transaction, and administrator behavior.
- Instant protective actions such as step-up verification, hold, freeze, or controlled delay on risky events.
- Continuous change-control watch over rules, limits, user rights, and sensitive configuration edits.
- Evidence preservation so investigations, complaints, management review, and regulatory response are grounded in complete records.
- Clean operational handoff from automated night monitoring into daytime fraud, risk, operations, and support workflows.
6. What top management should ask before scaling further
- Can we detect and stop a suspicious midnight disbursement before it settles?
- Can we distinguish a legitimate customer from an impersonator using the same credentials?
- Can we see and control privileged user actions, configuration changes, and limit edits after hours?
- Can we generate receipts, statements, complaint records, and investigation evidence without manual reconstruction?
- Can we prove business continuity, data protection discipline, and clean recovery if the night goes badly?
- Can our executive team explain the control model to the board in plain language?
The executive takeaway
For a CBK-licensed digital lender, the next competitive advantage is not only faster origination. It is trusted after-hours control. The institutions that win will be the ones whose backend can recognize abnormal behavior, protect customers, preserve evidence, survive disruption, and recover cleanly when the attack comes at midnight rather than midday.
Prepared as a leadership-oriented website blog draft for CBK-licensed digital credit providers and fintech leaders thinking beyond onboarding and growth into the harder question of after-hours control, digital resilience, and midnight fraud defense.

Leave a Comment