Executive View | Core Banking Leadership
Why Core Banking Systems Are a Headache for CIOs
Why the institutions that win the next era of banking will move beyond brittle cores, raw logs, and risky change cycles toward modular architecture, disciplined microservices, and self-reporting operational platforms.
For CIOs, CTOs, and senior management bankers | April 2026 | Editorial feature
Core banking systems are not just enterprise applications. They are the operational heart of a financial institution. They carry deposits, loans, payments, ledgering, reconciliations, channels, reporting, controls, and regulatory expectations all at once. That is why they become such a persistent headache for CIOs. When a core platform performs well, it feels invisible. When it begins to strain, every business line feels the impact immediately.
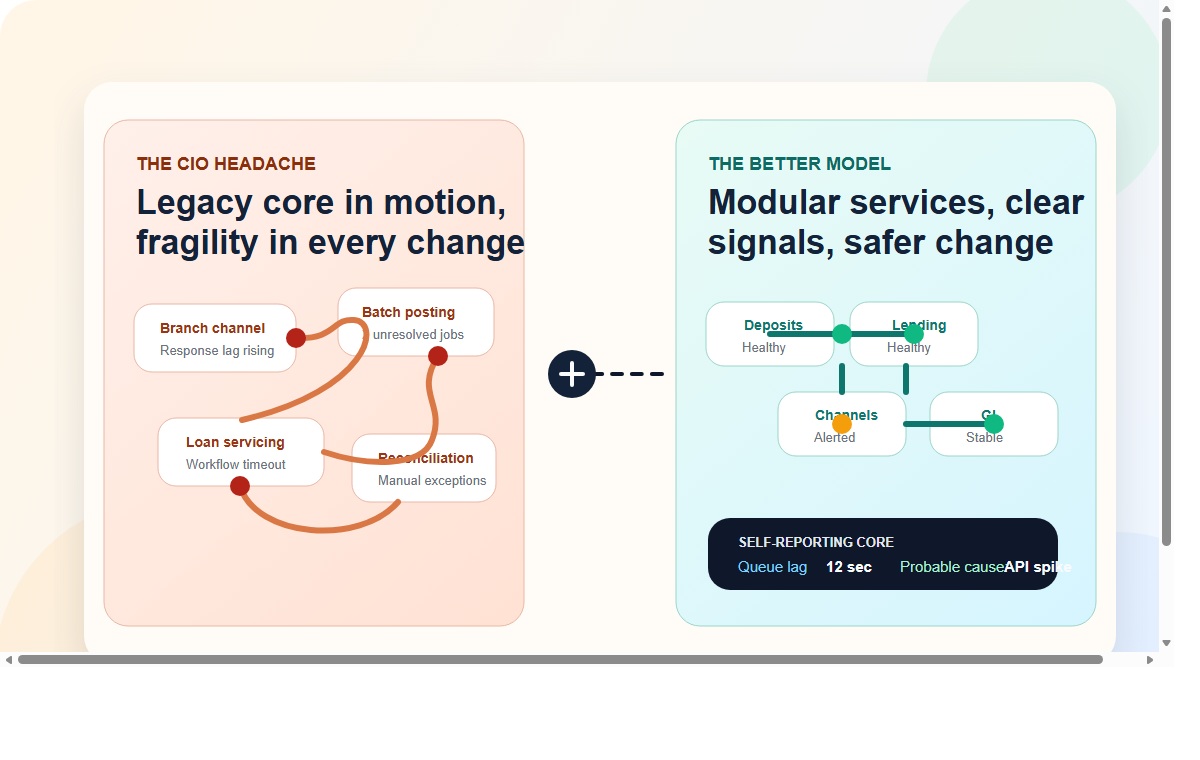
Every change is high-risk when service boundaries are weak and too many business functions are tightly coupled in one stack.
Every outage is amplified because the core affects customer experience, branch operations, liquidity visibility, accounting integrity, and management reporting at the same time.
Every blind spot is expensive when teams have logs after the fact, but not system signals that explain business risk in real time.
1. The real pain is architecture, not just functionality
Most CIO frustrations do not start with missing features. They start with architectural fragility. Many core banking environments were built over time through upgrades, customizations, patches, interfaces, and workarounds. The result is often a platform that still transacts, but no longer changes safely.
A simple pricing update can trigger broad regression testing. A channel issue can expose deep coupling in transaction logic. A reporting delay can trace back to design decisions buried years earlier. Over time, the CIO inherits not just a system, but an accumulated operating risk.
This is why many core platforms feel heavy even when they appear stable. The institution is no longer managing a flexible operating backbone. It is managing a fragile center of gravity.
“The CIO problem is rarely that the core cannot do enough. It is that the institution no longer trusts how safely it can change.”
2. Microservices only help when they are disciplined
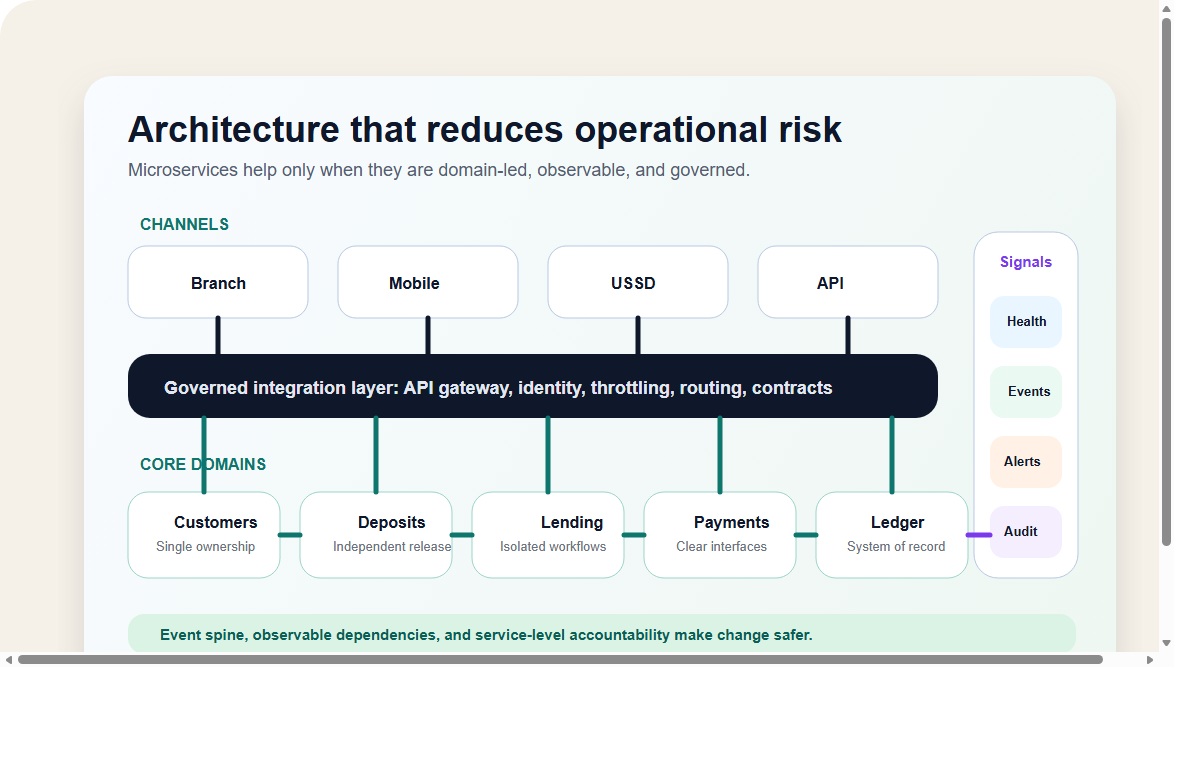
Microservices are now a common promise in banking technology discussions, but CIOs do not gain much from microservices as a slogan. They benefit only when the design is disciplined. Breaking a monolith into dozens of poorly governed services can simply create a distributed version of the same chaos: more moving parts, more dependencies, more operational overhead, and more things to monitor badly.
The better approach is domain-led architecture. Customer management, deposits, lending, payments, pricing, workflow, notifications, and ledgering should have clear ownership boundaries. APIs should be stable, versioned, and governed. Data ownership should be explicit. Dependencies should be visible. Failure in one peripheral service should not destabilize the transaction engine for the whole bank.
In practical terms, the right microservices strategy is not about multiplying components. It is about isolating change. CIOs need architectures where one business domain can evolve without forcing the entire institution into a high-risk release event.
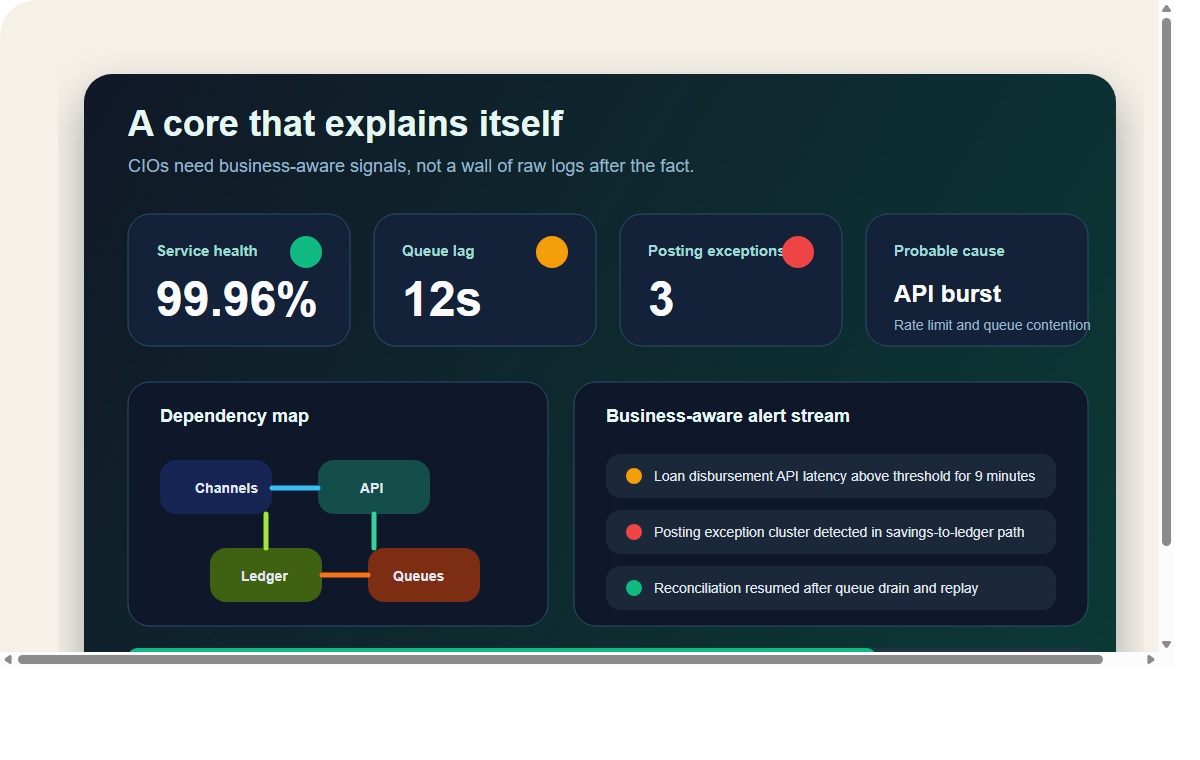
3. The modern CIO needs observability, not just logs
Another reason core systems become a CIO headache is that many of them remain operationally opaque. They generate logs, but they do not explain themselves. That distinction matters. Logs tell engineers what happened somewhere in the stack. CIOs need to know what business capability is now at risk, how large the impact could become, and where the failure is likely to propagate next.
In a modern banking environment, raw logs are no longer enough. A self-aware core should surface live service health, interface status, queue lag, transaction exception clusters, workflow bottlenecks, reconciliation breaks, configuration drift, and probable-cause signals. It should help operations teams and leadership understand not just that something failed, but what it means for the institution right now.
This is where system self-reporting becomes essential. Instead of asking teams to sift through logs after customers have already been affected, the platform should proactively tell the bank what is slowing down, what is stuck, what is degrading, and what part of the business service chain requires intervention.
4. Providers need to sell reduced operational risk, not just more features
System providers often make the wrong pitch to CIOs. They sell feature breadth when the institution is actually buying risk reduction. The stronger commercial argument is not simply that the platform can do more. It is that the platform can change more safely, scale more predictably, and make operations more intelligible.
That means vendors should design for resilience from the start. They should present clear service boundaries, governed APIs, event-driven patterns where they add value, explicit auditability, controlled configuration management, and observability that is tied to actual banking operations. A system should not merely produce telemetry. It should interpret that telemetry into operational insight.
CIOs increasingly judge platforms on questions like these: Can the core isolate failure? Can it expose dependency chains? Can it explain why a service is degrading? Can it support new products without destabilizing legacy ones? Can it modernize in layers rather than through one dramatic and risky replacement?
5. The right modernization model is layered, not theatrical
Most banks do not need a modernization slogan. They need a modernization path. The CIO headache grows worse when providers push a dramatic transformation story without respecting operational reality. Core renewal works better when it is composable: a governed integration layer, a digital onboarding layer, modular product factories, a strong ledger, workflow services, reporting services, and a clear monitoring and alerting fabric around them.
That approach gives institutions room to modernize without causing institutional shock. It also allows boards and executive teams to see technology change as a controlled strategic program rather than a high-stakes gamble.
What systems providers should be building into the platform
- Domain-based architecture with clear ownership across customer, lending, deposits, payments, and ledger services.
- Governed APIs and integration contracts that make change predictable rather than fragile.
- Self-reporting operational dashboards that surface health, queue lag, exceptions, and dependency impact in real time.
- Business-aware alerting that points to likely causes instead of forcing teams into post-incident log archaeology.
- Layered modernization options so institutions can replace and upgrade capabilities without destabilizing the whole core.
6. What the CIO ultimately wants is confidence
At the highest level, CIOs are not asking for complexity dressed up as innovation. They are asking for confidence. Confidence that the system can scale. Confidence that a new product launch will not trigger unintended failures. Confidence that if something begins to degrade, the platform will surface it early in language the institution can act on. Confidence that the provider understands core banking not as software deployment, but as institutional infrastructure.
That is why the next generation of trusted core banking platforms will not be defined by feature lists alone. They will be defined by architecture quality, observability maturity, microservices discipline, and self-reporting capabilities that make the institution easier to run rather than harder to decode.
The executive takeaway
Core banking systems become a headache for CIOs when they are tightly coupled, operationally opaque, and difficult to change safely. The providers that stand out will be the ones that treat architecture as a risk discipline, use microservices with restraint and clarity, and build self-reporting features that turn the core from a black box into an interpretable operating platform.
Prepared as a leadership-oriented website blog draft for CIOs, CTOs, and senior banking decision-makers. Copy is written for executive positioning and publishing readiness rather than academic publication.

Leave a Comment